In today’s validated lab environment, knowing the importance of an audit trail in computerized laboratory systems is just one of the integral qualification tasks that the ProPharma’s Computer System Validation (CSV) team focuses on for our clients. In this blog, we will briefly review the importance of providing assurances that your new or existing instrument software has a full audit trail system.
What is an Audit Trail?
The FDA defines an audit trail as, "a secure, computer generated, time-stamped electronic record that allows reconstruction of the course of events relating to the creation, modification, and deletion of an electronic record." What does an audit trail look like in practice?
An audit trail is a sequential record of events and changes that happen across your network, system, or trial. Every device in your network will create logs on the events it performs, an audit trail system will record all of these event logs. The information gathered can depend on industry or department, but most audit trail systems capture events by recording who performed an activity, what activity was performed, and how the system responded to this event. Because audit trails track nearly every change within a system, you will have a complete track record of your systems operations. Audit logs can be used to diagnose and troubleshoot issues, identify suspicious activity, and also give a great baseline for what a streamlined process looks like allowing for easy identification of fluctuations in your production chain.
Audit trails, while effective and efficient, are still a vulnerable system that can be compromised. Misconfigured, corrupted, or compromised say by a user who abuses their access or has access when they shouldn’t make the log useless. As a rule of thumb, the more human interaction you have with your audit trail, the greater the chance of human error. Smaller businesses can get away with more manual process of combing through devices, however larger businesses need the scale and reliability of audit trail software.
A Brief History of Audit Trails
First, a little history behind the need for a data audit trail. Almost six years ago FDA announced it would be conducting Part 11 audits alongside normal cGMP inspections to assess how industry interprets 21 CFR 11. According to FDA’s Pre-Approval Inspection Program 7346.832, the FDA inspector has to "audit the raw data, hard copy or electronic, to authenticate the data submitted in the [Chemistry, Manufacturing and Controls] CMC section of the application, and to verify that all relevant data (e.g., stability, bio batch data) were submitted in the CMC section such that CDER product reviewers can rely on the submitted data as complete and accurate."
Audit Trails Today
In recent years FDA has increasingly observed cGMP violations involving data integrity during inspections. This causes concern as data integrity is an important part of industry’s responsibility to ensure safety, efficacy, and quality of drugs, as well as FDA’s ability to protect public health. Some minimum requirements set forth by the cGMP to assure that drugs meet the standard of the FD&C Act regarding safety, identity, strength, quality, and purity in regards to data integrity include:
- Requiring that backup data are exact and complete, and secure from alterations, inadvertent erasures, or loss. As well as the output from the computer be checked for accuracy.
- Data be stored to prevent deterioration or loss
- Certain activities are documented at the time of performance, and laboratory controls are scientifically sound.
- Records be retained as original records or true copies, or other accurate reproductions of the original records.
- Complete information including data from all tests, complete records of all data, and complete records of all tests performed.
- Production and control of records be reviewed and that laboratory records be reviewed for accuracy, completeness, and compliance with established standards.
- Records be checked, verified, or reviewed.
The Benefits of an Audit Trail.
Proving Compliance
Audit trails are critical in order to maintain compliance with regulations such as HIPAA and PCI DSS. Audit logs can act as official records of business and can be used to prove compliance of regulations. Each regulatory body has specific standards when it comes to audit logs, HIPPA for example requires all logs to be maintained for a minimum of 6 years. These logs must be stored in a raw format for minimum 6 months to a year, after which they may be compressed. Be sure to review the specific compliance regulations for your business.
Gaining Insight
Audit logs give a high-level overview of your day to day business. Analyzing your audit logs can present the opportunity to boost performance, have increased accountability by your employees, and keep your business running smoothly. With the historical view provided by your audit logs, you can see operations that have improved in their efficiency or taken a hit. You can use this to find audit logs to find bottlenecks, providing data on how to make your entire business run smoother and more efficiently.
Improving Security and Fraud Prevention
Audit trails provide insight into security vulnerabilities or breaches and provide a monitoring system to track and identify these issues. Because audit logs work in concert with logical access controls, actions are able to be pinpointed to specific users and devices. If a user has been hacked or has its account privileges escalated giving an early warning sign of the security breach. Your logs will offer insight into files that were copied, printed, or even deleted keeping you in the know about specific data breaches and the next steps to correct the problem. Having an audit log system allows you to show your customers, partners, and regulatory bodies you are taking preventative steps to ensure the safety of their data and business.
In the world of computerized system validation, there exists an array of standalone PC based laboratory systems. The companies that manufacture and sell these systems bring efficiencies to the tasks of scientists, researchers and engineers. However, ensuring that data integrity needs are being met is typically a secondary objective when developing the application’s software. It is proving ever more difficult for compliance organizations to grasp the myriad ways in which these systems are configured to address the issue of data integrity.
Which leads us to the question, is the instrument’s operational software and file structure truly capable of providing the needed data audit trail? Remember, it is not only the system that must be validated but also the ability to trace the history of the data from its inception, through analysis, and potential reporting.
Audit Log Uses Example
The following Case Study involving an analysis lab system illustrates how the vendor of the software provided an audit trail an audit log vs as a true audit trail.
The system’s legacy PC was replaced with a 64 bit, Windows 7 Enterprise edition. The Vendor provided an upgraded version of their software that was compliant with the new OS. The audit component did indeed meet the NIST standards definition for audit trails;
- Evidence of the User’s credentials
- Date and time of log on and log off
- Machine identity
- Successful and failed attempts to access the system
- Files and networks accessed
- Changes to system configurations
- Use of system utilities
- Exceptions and other security-related events, such as alarms triggered
- Activation of protection systems, such as intrusion detection systems and anti-malware
However, this metadata that is being provided is no different than an event (audit) log that the Windows 7 operating system provides thru Microsoft’s Event Viewer, (Figure 1)
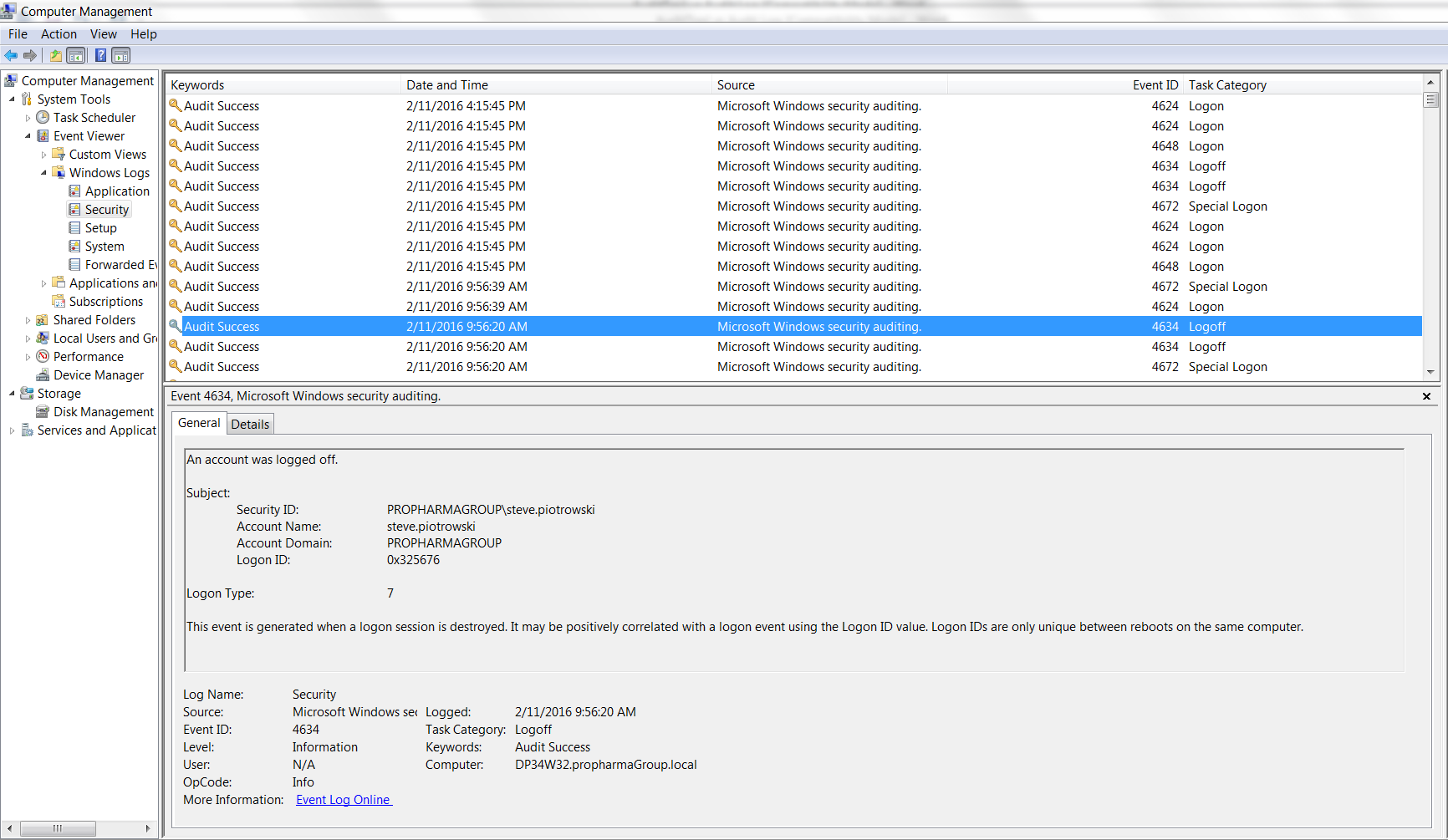
A pre-check prior to performing a scheduled supplemental IOQ revealed that no electronic record of the data’s lifecycle, e.g., creation, modifications, and/or deletions existed. Further investigation with the software supplier confirmed that their auditing was limited to system log files.
So, what do you look for to address this in a more compliant way? Well in this case, the primary limitation was that the data was stored in a flat file structure (Figure 2) as opposed to a RDBMS, (Figure 3)
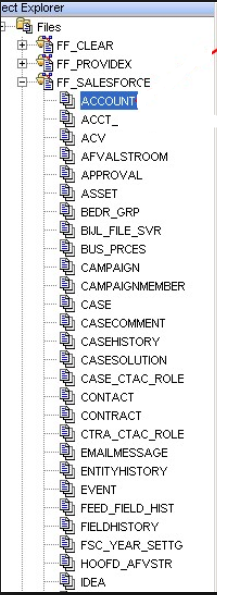
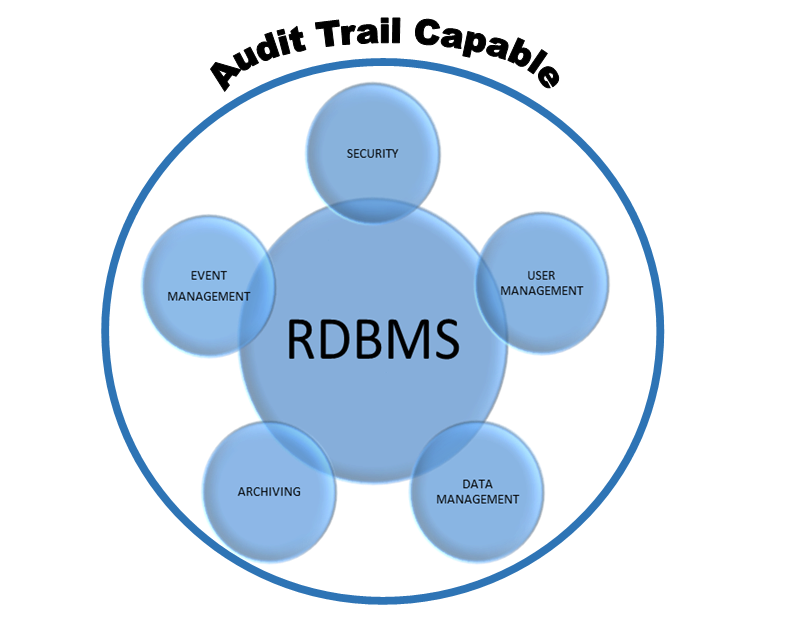
Figure 3 illustrates the concepts of a relational database, (e.g., MS Access, SQL). An RDBMS provides the capability of creating libraries. Libraries allow there to be individual data sets for auditable events such as data management and user management, but others can be configured as well. This allows the application architect to collaborate with the database architect to ensure that a fully compliant audit trail can be generated.
Still the best way to avoid finding yourself in the example given is to confirm with the Vendor that the data is stored in a RDBMS. If so, then ask if their standard audit queries the data’s event log. Answering yes to both of these questions will most likely mean happy audit trails for you.
Audit Logs and Your Business
With the benefits of audit trails, the next step is to implement the practice into your business. While this blog post serves as a guide on the steps to effectively implement a successful audit trail system within your business, you may need outside assistance to implement a system to your business and customers data protected and secure, as well as keeping your business in compliance.
Learn more about ProPharma’s CSV services.
Contact us to get in touch with our subject matter experts for a customized Computer Systems Validation presentation.
TAGS: Center for Drug Evaluation and Research (CDER) Good Manufacturing Practice (GMP) Computer Systems Validation (CSV) Health Insurance Portability & Accountability Act Current Good Manufacturing Practices (cGMP) Chemistry, Manufacturing, and Controls (CMC) Audit Trail Life Science Consulting
